In the era of information-driven businesses, safeguarding customer information has become paramount. However, an ongoing anomaly within organisations presents itself in the form of junior staff, such as customer service operators, having unfettered access to sensitive and privileged customer information. This information often includes financial data, passwords, transaction details, account numbers, names, addresses, and even dates of birth.
The fact that very junior staff often have access to such a wealth of critical information has raised serious concerns within industries. In this article, we will explore the insider risk associated with this practice, considering the necessity of this access, the potential threats, and the need for careful monitoring and control.
Essential Access and the Anomaly of Privilege
For many businesses to function smoothly, especially in sectors like banking, insurance, and telecommunications, providing access to sensitive information to customer service operators is essential. They must have immediate access to a wide array of personal and financial information to answer customer queries and resolve issues promptly.
However, this creates an ongoing anomaly, where the most junior members of the organisation have access to the most privileged information. The risk of misuse, accidental leakage, or intentional theft becomes a pertinent issue, which necessitates stringent monitoring and control.
The Need to Monitor Access
Companies need to pay close attention to what customer service operators are doing with the information they can access. What accounts are they accessing? What are they doing with the information? Is there a valid reason for them to be accessing specific customer details?
Implementing a robust monitoring system, including audit trails, can help in tracking user activities and identifying any suspicious behavior. Automated alerts for unusual activity patterns can be set up to provide immediate attention to potential insider threats.
The Danger of External Access to Internal Systems
The practice of allowing external access to internal systems can further escalate the risk. The temptation to misuse or steal information may become too great, especially when employees have the ability to access data from outside the company’s controlled environment.
There is also the increased risk of external hacking attempts when internal systems are made accessible externally. Security measures must be robust enough to deter both insider abuse and external threats.
Infiltration by Organised Crime Groups
Another alarming aspect of this situation is the instances of organised crime groups infiltrating organisations by gaining customer service positions. Once inside, they can potentially have access to a wealth of customer information.
Several high-profile cases have shown how criminal organisations have successfully placed individuals within companies, specifically in junior roles like customer service. From there, they can engage in data theft or fraud, causing significant financial and reputational damage to the businesses involved.
In Summary
The ongoing anomaly of very junior staff having access to highly privileged customer information is a complex issue that must be handled with great caution. While this access is often essential for businesses to function efficiently, it must be accompanied by rigorous controls and monitoring.
Organisations must strive for a delicate balance, ensuring that customer service operators can do their jobs effectively while mitigating the risk of data misuse. Robust monitoring systems, controlled access environments, thorough background checks, and ongoing training and awareness campaigns can go a long way in securing sensitive customer information.
The threat from both insider risks and organised criminal groups requires continuous vigilance. By recognising the risks and implementing comprehensive security measures, companies can protect both themselves and their customers from potential harm. Remember, in an interconnected world where data is the new currency, the weakest link in the chain might be the one handling the most valuable asset. Ensuring proper handling, monitoring, and control over who has access to sensitive information is not just best practice; it’s a business necessity.

Strategic Advisor, ShadowSight
Who is Christopher McNaughton
Chris is a proficient problem solver with a strategic aptitude for anticipating and addressing potential business issues, particularly in areas such as Insider Threat, Data Governance, Digital Forensics, Workplace Investigations, and Cyber Security. He thrives on turning intricate challenges into opportunities for increased efficiency, offering pragmatic solutions derived from a practical and realistic approach.
Starting his career as a law enforcement Detective, Chris transitioned to multinational organisations where he specialised and excelled in Cyber Security, proving his authority in the field. Even under demanding circumstances, his commitment to delivering exceptional results remains unwavering, underpinned by his extraordinary ability to understand both cyber and business problems swiftly, along with a deep emphasis on active listening.
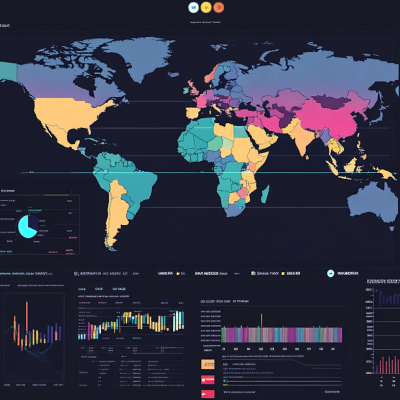
What is ShadowSight
ShadowSight is an innovative insider risk staff monitoring tool that proactively guards your business against internal threats and safeguards vital data from unauthorised access and malicious activities. We offer a seamless integration with your current systems, boosting regulatory compliance while providing unparalleled visibility into non-compliant activities to reinforce a secure digital environment. By prioritising actionable intelligence, ShadowSight not only mitigates insider threats but also fosters a culture of proactive risk management, significantly simplifying your compliance process without the overwhelming burden of false positives.