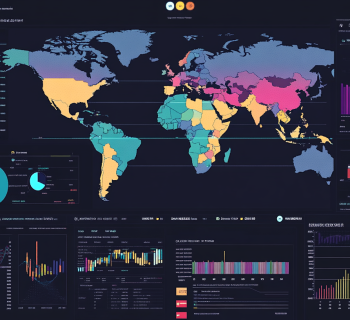
Cross-Border Data Flows: Navigating Challenges and Regulatory Requirements for Australian Organisations
In an era where data is as valuable as currency, the flow of information across international borders has become a critical component of global business operations. Australian organisations, in particular, face a unique set of challenges and regulatory requirements when transferring data across borders, especially in light of the Australian…