In today’s digital age, the significance of insider risk management cannot be overstated. With the escalating complexity of cybersecurity threats, organisations are increasingly vulnerable to the risks posed by their own employees, whether through malice, negligence, or mere oversight. An effective insider risk management program stands as a critical safeguard, mitigating these risks and ensuring the integrity of organisational data. This article delves into the essential features of an insider risk platform, highlighting how such platforms, exemplified by solutions like ShadowSight, are instrumental in fortifying organisations against the multifaceted threats from within.
Integration with Other Systems
Seamless integration with existing IT ecosystems is paramount. An insider risk platform should effortlessly connect with a variety of systems such as HR databases, Email, Financial systems, and other security tools. This integration enhances the platform’s ability to draw meaningful insights from a wide array of data sources, thereby improving its effectiveness in detecting potential risks.
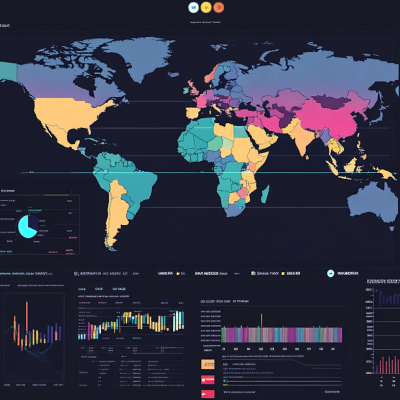
Insider Threat Dashboard
At the heart of an effective insider risk platform lies the Insider Threat Dashboard. This centralised hub provides a comprehensive overview of all insider threat activities, facilitating near real-time monitoring and analysis. It enables IT professionals and business executives to quickly grasp the security posture of their organisation, identifying potential threats at a glance.
Behaviour Analytics
Behaviour analytics stands as a cornerstone feature, leveraging advanced analytics to identify unusual behaviour patterns that may signify insider threats. By analysing user activities and comparing them against established baselines, the platform can flag actions that deviate from the norm, enabling pre-emptive measures to mitigate risks.
Forensics
In the unfortunate event of a security incident, forensic capabilities are crucial for uncovering the root cause and extent of the breach. An insider risk platform should offer detailed forensic tools to facilitate thorough investigations, ensuring that lessons are learned, and future incidents are prevented.
PDF Reporting and Scheduled Global Report Emails
Comprehensive reporting features, including PDF reporting and scheduled global report emails, are essential for keeping stakeholders informed. These features ensure that detailed, actionable insights are readily available, enabling informed decision-making and timely response to potential threats.
Data Protection
Data protection is the foundation of any insider risk management program. The platform should offer robust mechanisms to safeguard sensitive information from unauthorised access or theft, including encryption, access controls, and data loss prevention techniques.
Reporting & Analytics
Advanced reporting and analytics capabilities allow organisations to delve deeper into the data, uncovering trends and patterns that may indicate potential risks. These insights are invaluable for continuously improving security strategies and risk management practices.
Risk Score and Custom Policies
Assigning risk scores to users and implementing custom policies tailored to specific organisational needs are crucial features. They enable the platform to prioritise threats and customise its response, ensuring that resources are focused where they are needed most.
Alerting
Timely alerting mechanisms are critical to ensure that potential threats are promptly addressed. The platform should offer configurable alerts that can be tailored to the severity of the threat, ensuring that the right people are notified at the right time.
Flexible Deployment
Organisations have diverse needs, and an insider risk platform must offer flexible deployment options, including cloud-based, on-premises, and hybrid models. This flexibility ensures that the platform can be seamlessly integrated into any IT environment.
Scalability
As organisations grow, their insider risk management solutions must scale accordingly. Scalability ensures that the platform can handle an increasing volume of data and a growing number of users without compromising performance.
Content Inspection
Content inspection capabilities are essential for identifying sensitive information in communications and files. This feature helps in preventing data leaks and ensuring that only authorised personnel have access to critical data.
User Education
An often overlooked but vital aspect of insider risk management is user education. The result of alerts from the platform should ultimately educate employees about security best practices and the importance of safeguarding organisational data.
Workflow
Efficient workflow management is crucial for responding to and managing insider threats. The platform should provide tools for creating, tracking, and managing incidents, ensuring a coordinated and effective response to any threat.
Privacy Protection
In the process of monitoring and managing insider risks, it is imperative to protect the privacy of employees. The platform must include mechanisms to ensure that monitoring and data collection practices are compliant with privacy laws and ethical standards.
The Imperative of Insider Risk Management
The absence of a robust insider risk management program exposes organisations to significant dangers. Insider threats can lead to financial losses, reputational damage, and legal ramifications. Conversely, the implementation of an insider risk management program, equipped with the features outlined above, offers numerous benefits. It enhances organisational security, protects against data breaches, ensures compliance with regulatory requirements, and fosters a culture of trust and transparency. As organisations navigate the complexities of the digital landscape, the importance of insider risk management cannot be understated. Features such as an Insider Threat Dashboard, Integration with other systems, Behavior Analytics, and Data Protection, among others, are indispensable in a comprehensive insider risk platform. By prioritising the implementation of such platforms, organisations can significantly mitigate the risks posed by insider threats, securing their future in an ever-evolving digital world.
Strategic Advisor, ShadowSight
Who is Christopher McNaughton
Chris is a proficient problem solver with a strategic aptitude for anticipating and addressing potential business issues, particularly in areas such as Insider Threat, Data Governance, Digital Forensics, Workplace Investigations, and Cyber Security. He thrives on turning intricate challenges into opportunities for increased efficiency, offering pragmatic solutions derived from a practical and realistic approach.
Starting his career as a law enforcement Detective, Chris transitioned to multinational organisations where he specialised and excelled in Cyber Security, proving his authority in the field. Even under demanding circumstances, his commitment to delivering exceptional results remains unwavering, underpinned by his extraordinary ability to understand both cyber and business problems swiftly, along with a deep emphasis on active listening.
What is ShadowSight
ShadowSight is an innovative insider risk staff monitoring tool that proactively guards your business against internal threats and safeguards vital data from unauthorised access and malicious activities. ShadowSight transforms insider threat management by integrating Security Information and Event Management (SIEM) with behavioural analytics. This powerful combination dynamically adapts to both business operations and employee behaviours, efficiently identifying activities that pose organisational risks. This Australian innovation streamlines threat detection with user-friendly interfaces, eliminates ongoing professional services, and integrates seamlessly into existing business processes. It efficiently filters activities, applies custom rules, and offers comprehensive visibility through a single pane. ShadowSight provides a smarter approach to safeguarding against insider threats, distinguishing itself as the leader in adaptive security solutions.